What Is NIS2?

NIS2 is the European Union’s updated cybersecurity directive. It expands on the original NIS rules and raises the bar for how organizations manage cyber risk, report incidents, and protect critical systems and services.
In plain English, NIS2 is the EU making it clear that organizations providing essential or important services need to take cybersecurity more seriously, both technically and operationally.
It applies to more sectors and organizations than the original directive and places greater responsibility on leadership. That includes risk management, cyber hygiene, reporting obligations, and staff training.
Why Cybersecurity Training Matters Under NIS2
This is where a lot of organizations get it wrong.
They treat cybersecurity training as a separate awareness exercise while the “real” compliance work happens somewhere else. NIS2 does not support that thinking.
Cybersecurity training and basic cyber hygiene are part of the broader risk management picture. That means training is not just there to tick a box. It is there because staff behavior, weak habits, poor reporting, and everyday mistakes are still some of the easiest ways for attackers to get in.
You can spend a fortune on security tools, but if someone still clicks a fake invoice or hands over credentials to a polished phishing email, those controls can be undermined very quickly.
What Are NIS2 Cybersecurity Training Requirements?
NIS2 doesn’t hand organizations a checklist that says, “Run one course per year and congratulations, you are compliant.”
Instead, it takes a broader risk-based approach to cybersecurity.
The expectation is that organizations build appropriate risk-management measures into their operations. In practice, that means training should not be random, one-off, or disconnected from actual risk.
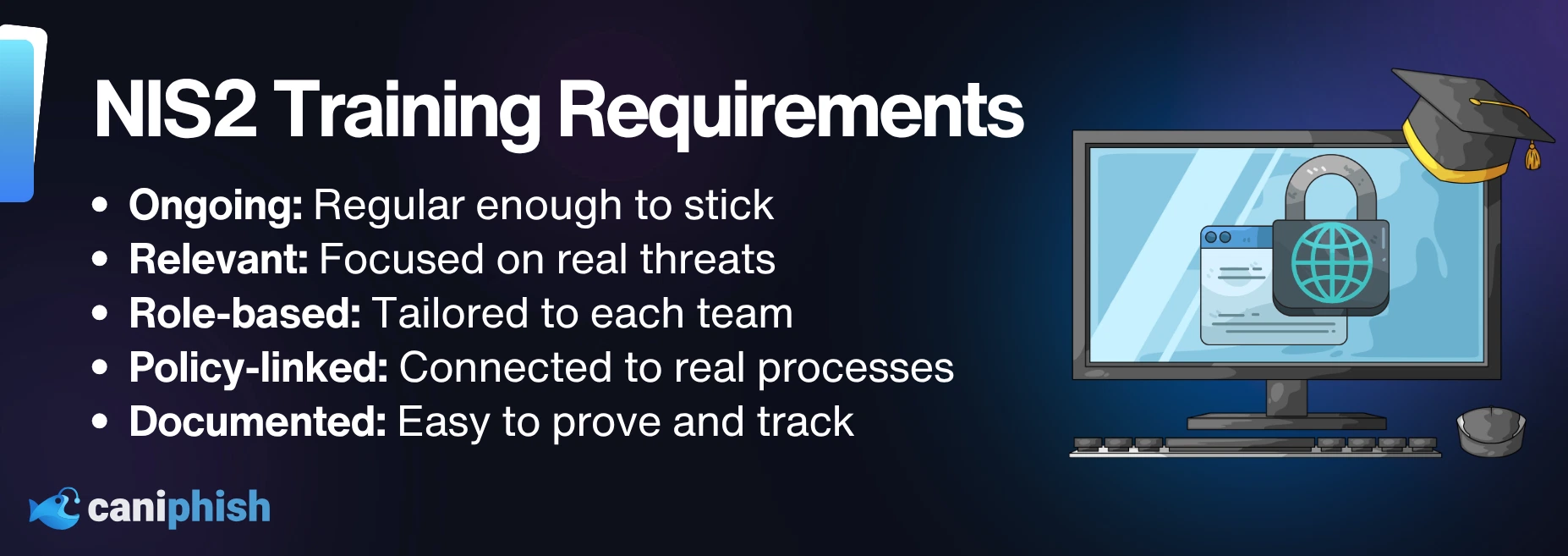
A stronger NIS2-aligned training program should be:
- Ongoing: This shouldn’t be the kind of training people see once a year, click through at speed, and forget almost immediately. It needs to show up often enough to stay useful.
- Relevant: Training should deal with the threats people are actually likely to run into. If it feels generic, outdated, or disconnected from real life, most staff will tune it out.
- Role-based: Not every team is dealing with the same threats, so not every team should get the same training. Finance, HR, leadership, and IT all deal with different risks, and the examples should match that.
- Policy-linked: Training should connect back to your real security rules and reporting processes, so staff know what is expected in practice and not just in theory.
- Documented: If your program exists, you should be able to prove it without digging through twelve folders and a panic-induced spreadsheet.
What Does “Basic Cyber Hygiene” Actually Mean?
Basic cyber hygiene sounds basic, but it covers a lot more than warning staff not to click dodgy links and hoping for the best.
It is the everyday security stuff that keeps small mistakes from becoming major incidents. That includes spotting phishing emails, using proper passwords, turning on MFA, being careful with attachments, reporting suspicious activity quickly, and not treating company systems like the Wild West.
None of it is flashy. That is kind of the point. It is just the practical day-to-day behavior that helps stop avoidable incidents before they become expensive ones.
In other words, basic cyber hygiene is the cybersecurity equivalent of brushing your teeth. It is not exciting, but ignoring it creates expensive problems.
Real-World Examples Of Why NIS2 Training Matters
A lot of cyber incidents don’t start with some movie-villain hacker hammering away in a dark room full of green code. They start with ordinary mistakes. Someone trusts the wrong email. Someone skips a verification step. Someone sees something suspicious and does nothing because they are not sure what the reporting process is.
A finance team is a good example. One fake supplier email lands in the inbox asking for updated bank details. It looks normal enough, sounds urgent enough, and catches someone at a busy moment. That is all it takes. If the team has not been trained to stop, check it properly, and know how to raise the flag, a very ordinary scam can turn into a very expensive mistake.
Senior leaders are no different. In some ways, they are worse off. They get targeted with messages that look urgent, confidential, and important because attackers know executives can move quickly and skip steps without even meaning to. If leadership is left out of training because they are “too busy,” that is not a strong security culture. That is just leaving a very obvious door open.
Then there is the new starter problem. A new employee joins, gets access on day one, and within a week gets hit with a fake login page or suspicious message. If they haven’t had proper onboarding and do not know what good security behavior looks like yet, they are far easier to catch out. ENISA’s (European Union Agency for Cybersecurity) implementation guidance points toward regular awareness raising and clear cyber hygiene practices for employees, including new staff, because attackers do not politely wait until onboarding is complete.
Why Ongoing Training Matters Under NIS2
Under NIS2, cybersecurity training is not supposed to be a one-time event that gets wheeled out once a year, half-watched, and forgotten by Monday.
The point is to keep security awareness active. Threats change, scams get better, staff roles shift, and new people join the business all the time. If training stays frozen while everything else moves, it starts becoming background noise instead of a real control.
If threats keep changing but the training does not, people stop seeing it as useful and it becomes much less effective.
7 Steps To Meet NIS2 Cybersecurity Training Requirements
If your organization falls under NIS2, these seven steps will help you build a training program that actually lines up with NIS2 and makes sense in the real world.
1. Confirm Whether NIS2 Applies To Your Organization
Before building anything, confirm whether your organization falls within scope. NIS2 covers more sectors and entities than the original directive, but the exact details still depend on how it is applied in the relevant member state.
2. Treat Training As A Security Control
Don’t treat training like a side project for compliance admin. It should be part of your actual risk management strategy, just like access controls, incident response, or supplier reviews.
3. Make It Ongoing
One training session per year is not much of a defense plan. Build a program that runs over time and gets refreshed regularly. That could include onboarding, refreshers, short awareness campaigns, and updates tied to new risks or incidents.
4. Focus On Practical Cyber Hygiene
Cover the issues staff are most likely to face. Phishing, suspicious links, weak passwords, MFA, reporting channels, safe system use, and basic social engineering awareness. If the training is too vague to apply in real life, it’s probably ineffective.
5. Tailor It To Different Roles
A finance team faces different threats than HR. Executives face different threats than general staff. Role-based training is far more useful than blasting everybody with the same generic content.
6. Include Leadership
NIS2 puts more responsibility on management, so leadership should not be floating above the training program like they are somehow immune to phishing. They are often the most heavily targeted.
7. Keep Records And Review It
Document what training was delivered, who completed it, what roles were covered, and when the content was updated. If you cannot show evidence, your program is much harder to defend.
Wrapping Up
NIS2 makes it harder to treat cybersecurity training as an afterthought. The point is not to throw more content at staff just to look compliant. It is to make sure people know what to do when something looks off. If the training helps people spot suspicious activity, follow the process, and avoid preventable mistakes, it is doing what it should.
The 7 Types Of Phishing Websites
Discover the 7 types of phishing websites cybercriminals use.
Learn how to spot them